An advanced persistent threat (APT) hacking group operating with motives that likely align with Palestine has embarked on a new campaign that leverages a previously undocumented implant called NimbleMamba.
The intrusions leveraged a sophisticated attack chain targeting Middle Eastern governments, foreign policy think tanks, and a state-affiliated airline, enterprise security firm Proofpoint said in a report, attributing the covert operation to a threat actor tracked as Molerats (aka TA402).
Notorious for continuously updating their malware implants and their delivery methods, the APT group was most recently linked to an espionage offensive aimed at human rights activists and journalists in Palestine and Turkey, while a previous attack exposed in June 2021 resulted in the deployment of a backdoor called LastConn.
But the lull in the activities has been offset by the operators actively working to retool their arsenal, resulting in the development of NimbleMamba, which is designed to replace LastConn, which, in turn, is believed to be an upgraded version of another backdoor called SharpStage that was used by the same group as part of its campaigns in December 2020.
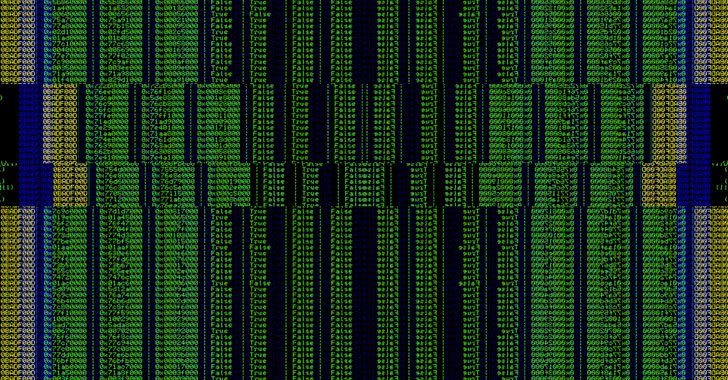
“NimbleMamba uses guardrails to ensure that all infected victims are within TA402’s target region,” the researchers said, adding the malware “uses the Dropbox API for both command-and-control as well as exfiltration,” suggesting its use in “highly targeted intelligence collection campaigns.”
